Ensuring data and technology reliability
Data and technology are only useful if they are reliable. ITGC and GITC help to assure key members of your organization as well as external parties such as regulators, audit committees, and auditors, that business processes and data are being used with integrity.
ITGC and GITC also help with financial audits by helping to ensure information is not altered, minimizing the risk of fraud, waste, and abuse.
A recent report from Deloitte identified six key reasons why ITGC and GITC are important tools for ensuring integrity in business operations and reporting
- Well-managed organizations are built on effective controls that ensure streamlined operations functions, legal and regulatory compliance, and proper financial reporting.
- Management can only drive business performance and decision-making using reliable processes and financial data.
- Business organizations face increasing complexity when it comes to financial reporting. The evolution of business also means more complex business models and technology.
- In today’s data-driven environment, regulators are expecting reliable financial information, while business stakeholders seek transparency and more specific information from business leaders.
- Reliable data and processes help protect organizations against the risk of cyber threats.
- Automated controls like access controls, segregation of duties, calculations, and input and output controls require standards like ITGC in order to function properly.
Risks caused by deficient controls
The risks of not having reliable data through proper ITGC or GITC implementation are numerous—and they are critical.
Poor internal controls hurt your ability to prepare and report accurate financial data, which can delay your financial closing process. Disclosure delays or potential data integrity issues can have a harmful effect on your organization’s brand and reputation. ITGC deficiencies may also increase the cost and effort needed for financial audits as additional audit procedures will be required. Most importantly, deficient internal controls could ultimately result in a financial misstatement that could have widespread implications throughout your organization.
Where to focus
So, if your organization is trying to implement more stringent internal controls, you might be asking yourself where to start.
Deloitte identifies three main areas to focus your internal control efforts:
- User Access Management: Understanding who has—and actually needs—access to key information is vital to ensuring data integrity.
- Change Management: It’s imperative that organizations have robust systems in place to track how information or processes are changed—and when those changes are accepted or rejected.
- Outsourced Service Provider Controls: With the use of outsourced technology service providers being a regular part of today’s global business environment, businesses must be able to ensure those service providers are working with the proper controls to prevent potential data breaches or inaccuracies.
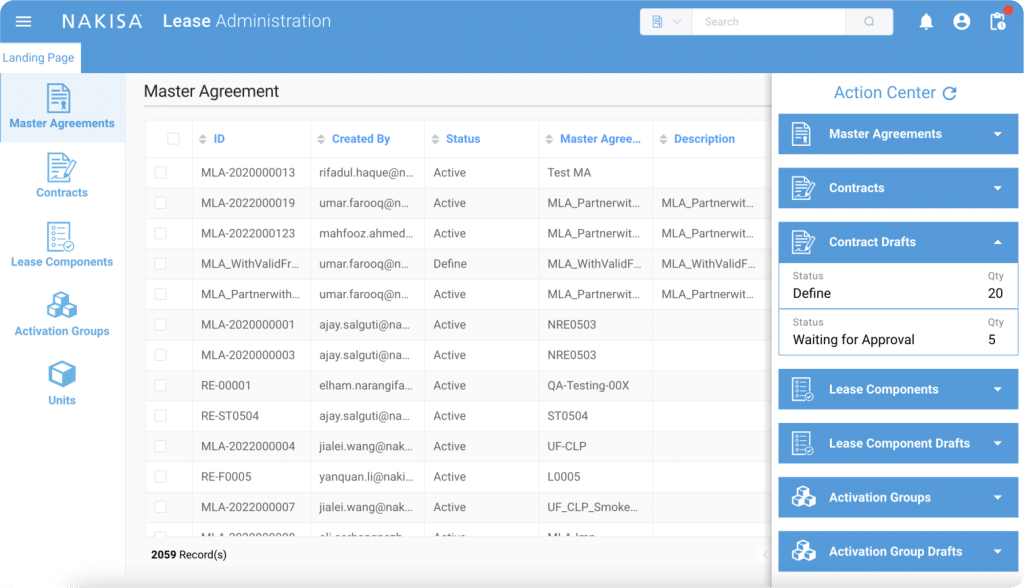
Nakisa Lease Administration, our industry-leading lease accounting software, helps support these three main areas of focus for ITGC. For user access management, Nakisa Lease Administration software provides predefined roles that describe access limitations such as who can access what information or who can change or edit information. For change management, Lease Administration provides an audit trail for both the frontend and backend. It also tracks who made a change, what change was made, and when the change was made. When it comes to outsourced service provider controls, Nakisa Lease Administration lets you assign a role to the outsourced provider as an Admin Power User, giving you access to the backend to troubleshoot software issues and providing view-only access to the front end.
As technology and data play an increasingly important role in your business, are you prepared to ensure the integrity and accuracy of your data and processes? Feel free to reach out to us. Our solutions engineers will be more than happy to share industry best practices with you, acquired through years of working with Fortune 1000 clients.