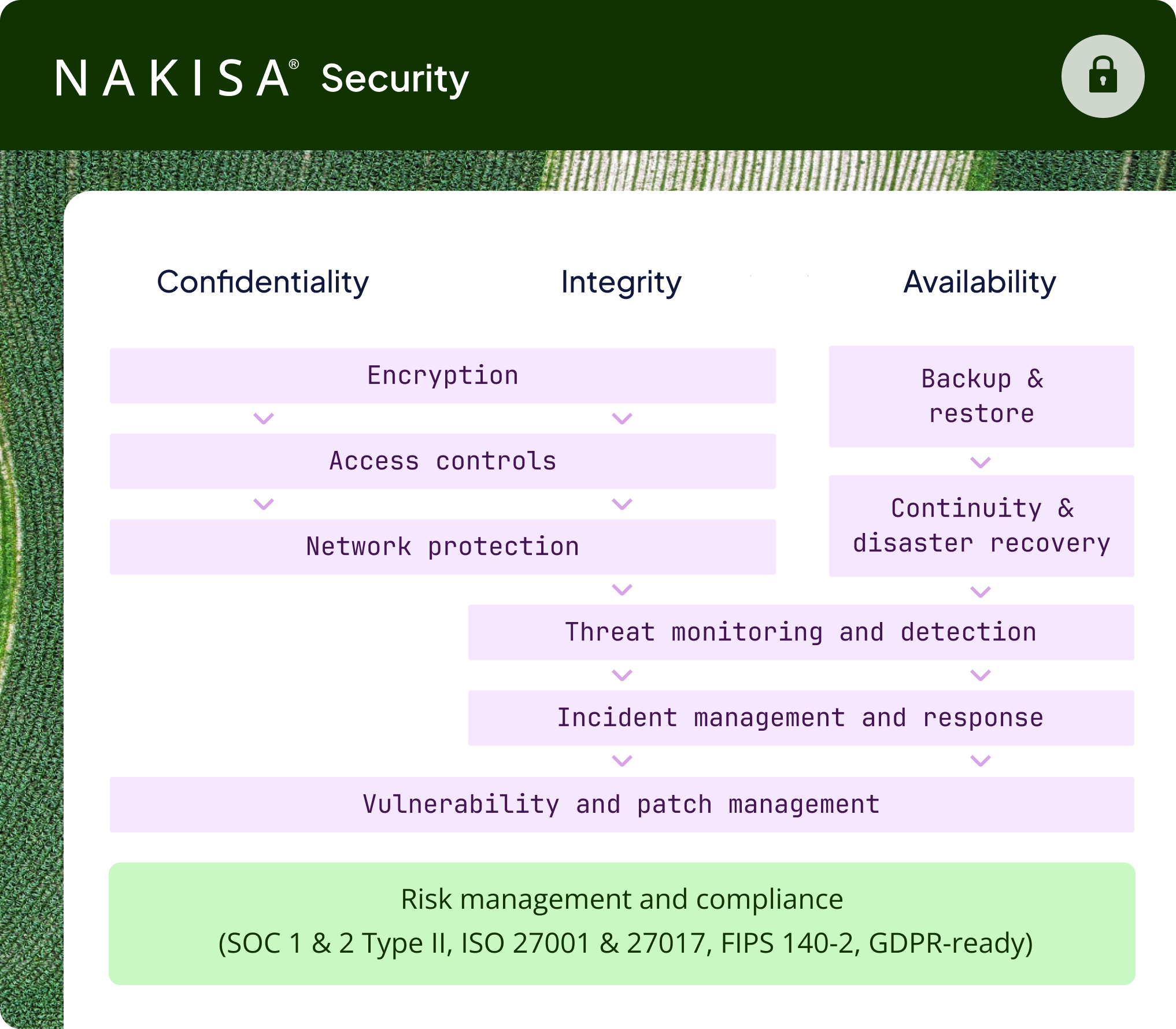
Nakisa security: your data in the best hands
- Data encryption in rest and in transit
- SOC 1 Type II & SOC 2 Type II audit reports
- ISO 27001 and ISO 27017 certifications
- GDPR requirements
- Role-based access control
- Single sign-on (SSO)
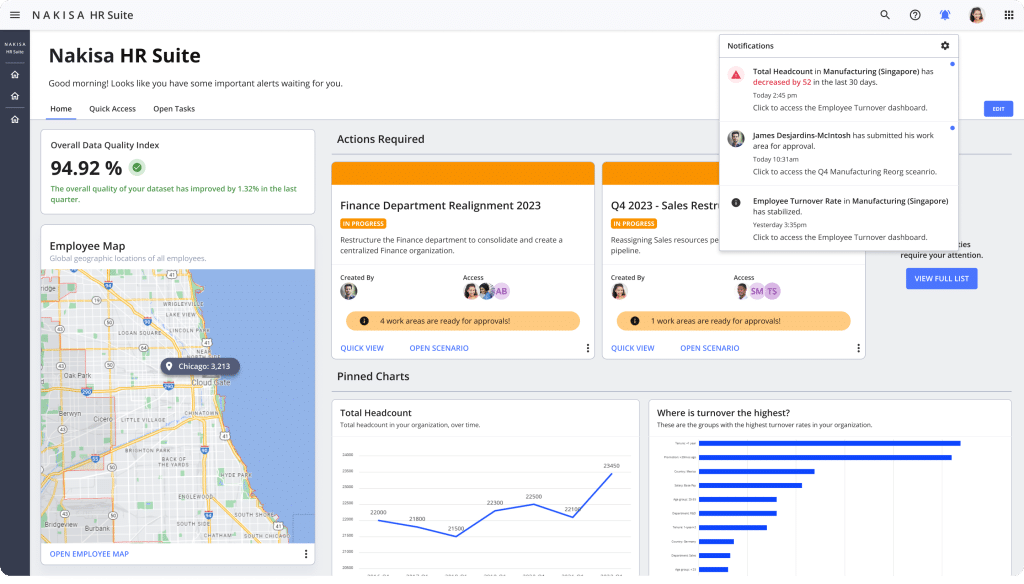
What is Nakisa
Nakisa is a cloud-native enterprise application provider that empowers lease accounting, workforce planning, and IWMS teams. Our business-critical solutions provide teams with insights, workflows, and automation so they can perform tasks efficiently and focus on more value-added activities.
To build our applications, we leverage state-of-the-art tech stacks and industry-proven methods such as Kubernetes, Kafka, CI/CD frameworks, and more. The foundation of what we create is the Nakisa Cloud Platform, a secure, flexible, API-driven cloud architecture that enables our clients to connect their finance solutions and ERPs like SAP S/4HANA to our products.
Our solutions include:
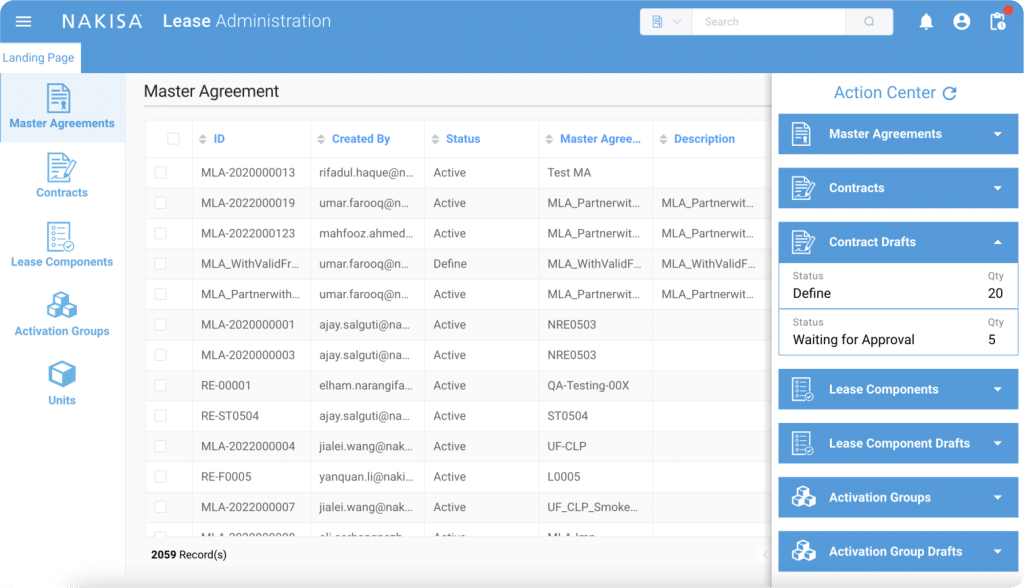
– Nakisa Lease Accounting: a solution for lessees and lessors to have full control over growing portfolios of leased assets and ensure compliance with IFRS 16, ASC 842, and GASB 87.
– Nakisa IWMS: a solution for real estate, finance, and facilities teams to oversee capital projects, manage enterprise portfolios, handle lease accounting, and streamline facility management.
– Nakisa Workforce Planning: a solution for HR professionals to manage workforce planning, organizational design, visualization, and analytics, as well enabling them to predict the effect of a future event on human capital.
Your security is our priority
Building trust means peace of mind. That’s why we promise our clients we’ll be their most trusted software partners—and we deliver on that. Nakisa uses the most established, industry-proven cybersecurity and risk management practices and resort to the leading technology services providers.
Also, our experts rigorously follow the latest industry standards to protect your data and systems at every stage of their lifecycles. This way, you can perform your daily operations and design your business strategy with all tranquility.
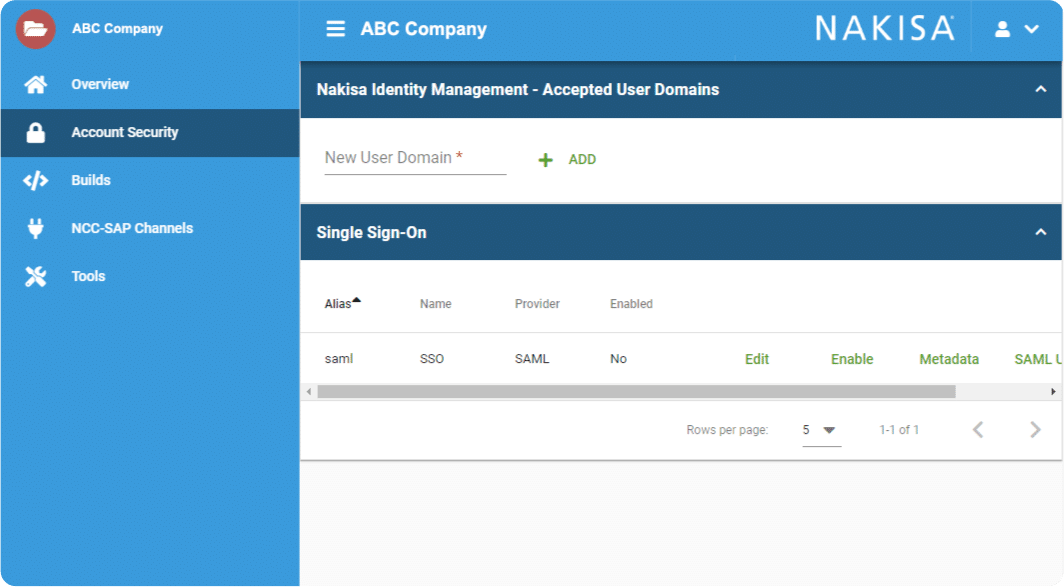
Welcome to our security cockpit
- Manage identities and access with out-of-the-box role-based access controls
- Run authentication mechanisms, including single sign-on (SSO) and multi-factor authentication.
- Monitor the state of their solutions and environments, ensuring everything runs smoothly for users.
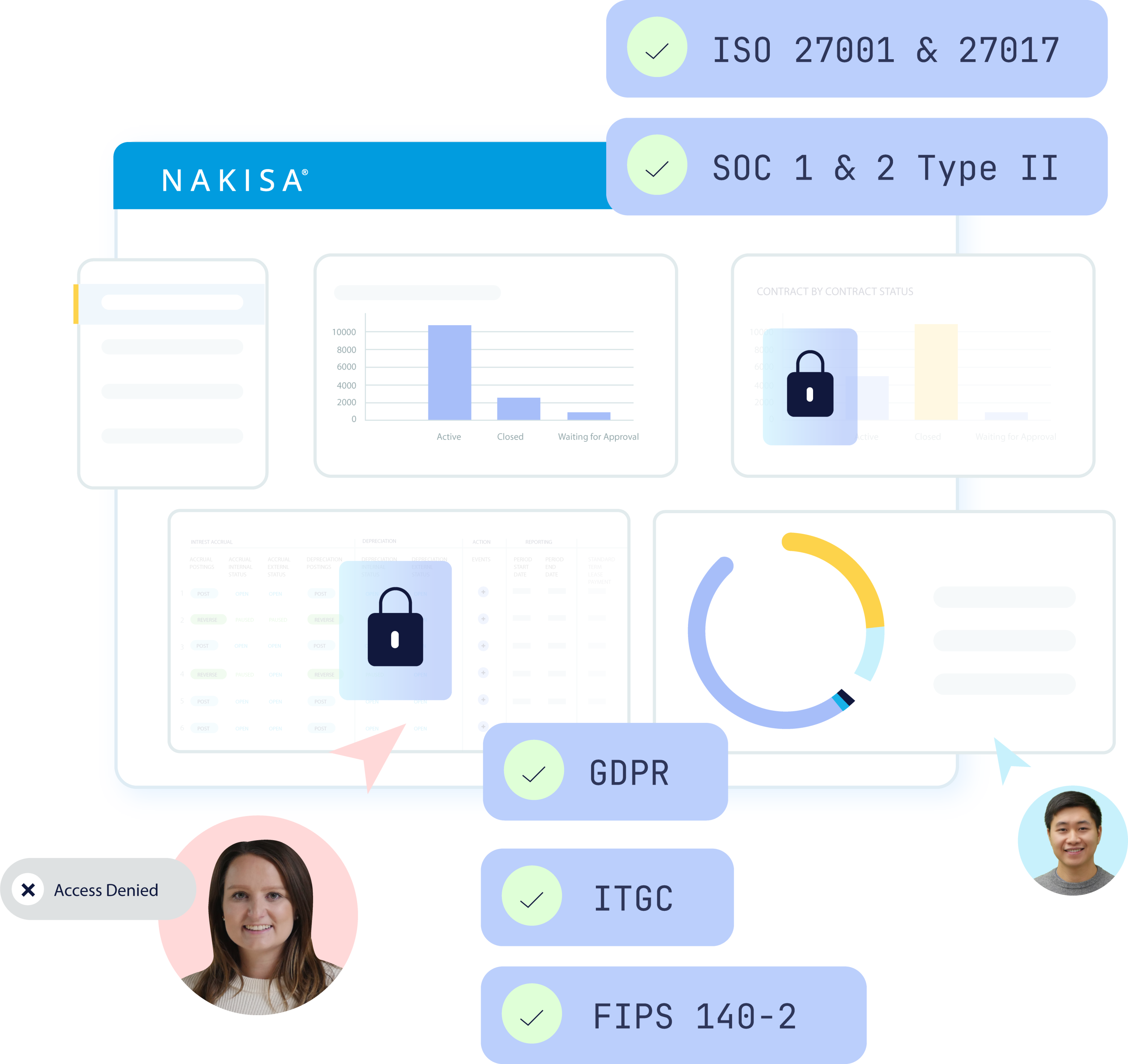
Certifications & audits
As the security and privacy of your data is our priority, we take every step necessary to assure our clients of this commitment. This includes voluntarily undergoing the lengthy process of independent third-party certification based on industry standards.
Nakisa undergoes annual SOC 1 Type II and SOC 2 Type II audits conducted by an independent third-party auditing firm. Our SOC 2 Type II report evaluates the design and operating effectiveness of controls aligned with the Security and Availability Trust Services Criteria.
As part of its ISO 27001 and ISO 27017 certifications, Nakisa strengthens its leadership in information security management and cloud security practices, highlighting its ongoing commitment to proactive risk management, compliance with international standards, and continuous investment in a secure infrastructure.
The above SOC and ISO reports, penetration test reports, and other certifications are available in December of each year to our partners and prospects upon request. To request any of our certifications or reports, click here.
GDPR requirements
- Search for records within the app, with support to remove specific information if needed.
- Providing our clients with configurable privacy and compliance settings such as using their own SSO, controlling who can access the application and what kind of information, and more.
- Providing sufficient data transfer methods to our clients.
- Maintaining records of processing activities.
- Training employees on security and privacy practices.
Our third-party security measures
Nakisa leverages leading global cloud infrastructure providers that implement robust physical and logical security controls across their facilities. These providers undergo regular independent audits and maintain a wide range of internationally recognized certifications to support secure and compliant cloud operations worldwide.
Depending on region and service scope, Nakisa’s cloud infrastructure providers maintain compliance with a range of international, regional, and industry-specific standards, including:
C5 [Germany]
Cyber Essentials Plus [UK]
DoD SRG, FedRAMP, FIPS IRAP [Australia]
ISO 9001, ISO 27001, ISO 27017, ISO 27018
MLPS Level 3 [China]
MTCS [Singapore]
SOC 1/2/3.
Encryption of data at rest and in transit
Encryption key management
Encryption of data at rest is supported through the secure key management services of our global cloud infrastructure provider. Encryption keys are generated, stored, and protected using industry-standard cryptographic controls and are managed by automated systems, reducing the risk of unauthorized access or human exposure.
Cryptographic operations are performed within the cloud provider’s secure environment, and encryption keys are never exposed to the application or to Nakisa personnel. The underlying key management service is validated against FIPS 140-2 standards, providing independent assurance of the confidentiality and integrity of cryptographic operations.
As part of Nakisa’s multi-tenant application architecture, customer data and databases are logically isolated to ensure strong separation between client environments.
User authentications and profiles
Nakisa’s authentication and authorization setup uses industry best practices and standards and allows clients to either leverage their own single sign-on or use Nakisa Identity & Access Management. Nakisa offers role-based access, meaning the clients can decide how to grant access to each user.
Single sign-on support
This single sign-on (SSO) login standard has significant advantages over logging in using application-specific usernames and passwords: no need to remember and renew passwords for each application, no weak passwords among others, and one credential for all applications to unify your personal password management, supporting your company’s password policy. The SSO is supported by configuring SSO via SAML2, which will authenticate and fetch roles and user population credentials. The fetched list of groups will be assigned to the logged-in user from your existing identity provider (for example, LDAP). The users will be validated through a SAML token, securely exchanged between the Identity Provider (IdP) server and the Nakisa application server. SAML allows for a seamless SSO experience between the client’s internal identity and access management solution and Nakisa solutions.
Nakisa Identity and Access Management (NIAM)
The Nakisa Identity and Access Management solution (NIAM) is available to clients who use Nakisa’s authentication system rather than SSO. It is a simple solution that allows organizations to easily manage their user’s provisioning and authentication to Nakisa’s SaaS solutions through a single platform. NIAM enables you to access your users through an enterprise-grade identity and access management solution while ensuring the right roles and profiles are assigned. Each role has different access privileges that can be individually assigned and limited by scope and duration. Whether you provide access to partners or employees from multiple subsidiaries worldwide, you’ll offer the same seamless experience your users expect while effectively managing the sensitive aspect of data access. Please get in touch with your Nakisa Account manager for more details about this solution.
Cloud infrastructure access and authorization
For greater security while accessing our cloud infrastructure, Nakisa uses role-based access controls to ensure that only authorized cloud engineers can perform specific tasks aligned with their job responsibilities. To access the cloud infrastructure, we utilize multi-factor authentication (MFA), which requires approval from different managers and heads of departments, with the final required approval from our Chief Security Officer.
In addition to our annual third-party SOC audit, and as part of Nakisa’s Access Management policy, internal audits are performed regularly to review such accesses and corresponding logs.
Application logs & auditing
In addition to our annual third-party SOC audit, and as part of Nakisa’s Access Management policy, internal audits are performed regularly to review such accesses and corresponding logs.
Logs are securely stored and protected from unauthorized modification. Access to log data is restricted based on defined roles and permissions to preserve integrity and confidentiality.
Logging practices are aligned with Nakisa’s security monitoring and incident management processes, enabling timely investigation and response to potential security events.
Dedicated, encrypted site-to-site integration through Nakisa Cloud Connector (NCC)
Nakisa uses industry best practices and standards to integrate our SaaS solutions with your internal ERP systems or any other data source so that you can leverage your data with our solutions.
The Nakisa Cloud Connector (NCC) enables integration between your ERP of choice and Nakisa SaaS applications with security and data integrity at its core. To ensure secure data transfers, NCC uses a two-way encrypted channel for all communication between ERP servers and Nakisa Cloud (using TLS over TCP), removing the need for back-channel VPN tunnels. The connector uses an ERP gateway to access the backend servers, enabling IT professionals to configure and leverage existing ERP infrastructure and security frameworks. Dedicated endpoints are provided for each client, completely isolating their communications with their on-premises ERP infrastructure.
We also provide you with the information needed to enable your IT team to allowlist Nakisa solutions to ensure the security of communication and data transfer.
Read more about NCC for Nakisa Finance Suite and NCC for Nakisa Workforce Planning users.
Nakisa AI technology
At Nakisa, safeguarding data while harnessing advanced AI capabilities is our top priority. Our approach to AI and Large Language Model (LLM) integration is built on a foundation of robust security, privacy, and data ownership principles, ensuring that every interaction remains secure, fully compliant, and entirely under the client’s control.
Robust AI model strategy
The Nakisa Cloud Platform leverages a robust Large Language Model (LLM) engine through a strategic and adaptable integration framework. Model selection is guided by key criteria including sustainable performance, completion accuracy, and response faithfulness, ensuring consistent value and reliability for enterprise use.
AI capabilities are seamlessly embedded across the platform’s microservices, powering a broad spectrum of features such as generative AI for dynamic content creation, intelligent search, predictive analytics, and automated workflows. Through Retrieval-Augmented Generation (RAG), the platform enhances response accuracy by dynamically retrieving relevant data, ensuring contextualized, real-time interactions. These capabilities enable data-driven decision-making, deliver personalized user experiences, and support proactive issue prediction—empowering organizations to address potential challenges before they impact operations.
API integration
Nakisa leverages secure API integrations to interact with external LLM services for inference processing. Prompt data—including user questions and AI interactions—is transmitted over encrypted channels to the LLM provider’s environment for transient processing, after which responses are returned to Nakisa. Nakisa does not persist or store customer prompt data outside its controlled infrastructure. Under the provider’s enterprise/API terms, submitted data is not used for model training and is not retained beyond the processing window. All input and output data retained by Nakisa are stored within Nakisa’s controlled environment, enabling full auditability, traceability, and alignment with enterprise-grade data governance and compliance requirements.
AI model training practices
Client data is never used to train third-party AI models. Nakisa continuously monitors AI performance, bias, and compliance while refining internal prompting workflows to improve results, ensuring insights remain reliable and responsible.
RAG methodology
At Nakisa, Retrieval-Augmented Generation (RAG) is a foundational component in delivering precise, context-aware AI interactions while maintaining strict data privacy standards.
RAG enhances the capabilities of the underlying Large Language Model (LLM) by dynamically retrieving relevant information from the client’s proprietary, indexed data in real time. When a user submits a query, the system identifies the most pertinent content and transforms it into vectorized representations—known as embeddings—which are then securely passed to the LLM. This allows the model to generate responses that are highly contextualized and aligned with the client’s specific business context, without relying solely on static model knowledge.
To support data privacy, Nakisa limits the data transmitted to the external LLM to the minimum information necessary to fulfill the request. Through its privacy-preserving RAG architecture, this may include the user’s query and selected, query-relevant content, while raw enterprise datasets and source documents in their entirety remain within Nakisa’s controlled infrastructure. Embeddings used in retrieval are generated internally within Nakisa’s environment and are non-human-readable vector representations. This architecture supports data isolation, customer ownership, and enterprise security and compliance requirements.
Secure Software Development Life Cycle (SSDLC)
Security is at the core of our software design. We’ve adopted numerous best practices and leverage the OWASP framework for our software development to ensure security by design right from the start.
Code review
All changes to our code are tested by our Quality Assurance (QA) team, and criteria are established for performing code reviews, web vulnerability assessments, and advanced security tests. We conduct manual and automated code reviews before checking in code. After code checks, the QA teams perform regression and functionality tests. In addition, we also use in-house and third-party solutions to conduct vulnerability assessments and security tests on our application. Vulnerability tests are carried out before each release, and as often as needed, where we test the solution to assess the application across its key functional and security components. Upon development, we deploy in a lower environment to enable stakeholders to test the solution before deployment in the production system. All such activities are recorded as part of our change management policy (please note that our auditors validate our enforcement of changes as part of SOC 2 audits).
Quality assurance
Each product release is put through a stringent functionality test, performance tests, stability tests, and UX tests before they are released. We validate the releases in internal builds followed by lower environments before pushing them to the production system following our change management policy.
Vulnerability assessment & penetration testing
- Cross-site request forgery (CSRF)
- Cross-site scripting (XSS)
- Improper input handling (SQL injection, XML injection…)
- HTTP response splitting
- Authentication and authorizations
Malware protection
Nakisa Cloud only uses non-Windows operating systems, and all systems follow a hardening baseline policy for security management. Note that our deployment architecture is based on DMZ, and no end-user access is available to server resources at the OS level. User-uploaded documents are not stored in the server file system and are not accessed at the server level. Network security controls, including firewalls and intrusion detection and prevention mechanisms, are used to protect inbound and outbound traffic. Application and platform monitoring capabilities support the detection and alerting of security-relevant events and system availability issues. All Nakisa employees use systems that have antimalware, supporting real-time scanning and security, and automatic updates are enabled on devices.
Security monitoring
We have various security measures and systems that continuously monitor for malicious activity, attacks, and unauthorized behavior from multiple perspectives. Our team can mitigate any potential attacks by following the internal procedure set for such events. We share our security systems, architectures, and test results with our SOC 2 auditing firm, and you can review such measures upon requesting the SOC report.
Business continuity, disaster recovery, and backups
Nakisa maintains a robust Disaster Recovery (DR) and Business Continuity framework designed to ensure the resilience and availability of our cloud solutions. In the event of a disaster that impacts service accessibility, our DR processes enable service restoration within our defined Recovery Time Objective (RTO), with data recoverable up to the defined Recovery Point Objective (RPO).
Our disaster recovery capabilities are regularly validated through scheduled tests and simulated scenarios to ensure readiness, verify backup integrity, and confirm that recovery procedures operate effectively.
Client production data is backed up daily and securely stored within the same geographic region in separate data center locations to support rapid recovery in the event of a disruption. Backups are periodically validated as part of our business continuity testing to maintain reliability and integrity.
Through our cloud infrastructure and automated recovery mechanisms, Nakisa ensures that services can be restored quickly and securely, providing our clients with continued trust, stability, and operational continuity.
Data sovereignty & transparency
Nakisa leverages a global network of cloud data centers strategically located across Canada, Germany, Singapore, the UAE, and the USA, demonstrating our commitment to providing secure, cloud-native, AI-powered solutions while ensuring compliance with local data sovereignty regulations. We emphasize transparency by giving clients complete visibility into their data’s storage locations, allowing them to choose their preferred region from a variety of options. Backed by strong partnerships with industry leaders like AWS and Microsoft, we deliver advanced, reliable, and secure technology solutions to enterprises around the world.
Incident management
Nakisa has an incident management policy that follows the industry standard depending on the priority of the incident and its effect on our clients, which is reviewed at least annually by an independent global auditing firm. Also, per the SOC 2 compliance and Nakisa’s Incident Management policy, a support case is triggered after each security incident, which details the incident and flags the appropriate level of urgency to address and resolve it. Resources are assigned as needed to each incident based on support triage to identify the root cause and proceed to resolution. In the event of a security incident, Nakisa follows defined containment and remediation procedures appropriate to the nature and severity of the incident, which may include isolating affected components to prevent further impact.
Nakisa Service Level Agreement (SLA) for security incidents and mitigations
In case of any potential or active security incident of which Nakisa is made aware, we address the security ticket following a priority level assessment – low, medium, high, or critical – based on the security incident’s impact on our clients. We provide different mitigation timelines in addition to daily updates and post-incident analysis documentation, where applicable, outlining root causes and preventative measures.
Physical perimeter security
The physical security of the infrastructure hosting Nakisa cloud solutions is managed by Nakisa’s cloud data center providers. These facilities implement layered physical security controls, including 24/7 security guards, perimeter protections, monitored access points, surveillance systems, and intrusion detection mechanisms. Physical access to sensitive areas is tightly restricted, logged, and subject to regular review in accordance with the providers’ security standards and independent audits.
Capacity management & load balancing
We leverage a global third-party provider’s services to offer on-demand and automatic capacity expansion and distribute traffic from our clients across multiple zones to support high availability. While ensuring no one server is overworked, which could result in degraded performance or unavailability (See “Availability” section for more details), you can instantly expand or reduce the capacity needed without technical support or additional investment in the infrastructure.
Cloud availability
We provide up-time of at least 99.5% for our Cloud (SaaS) clients with high availability. Using the latest cloud technologies enables us to increase resources on the run and ensure continuous system operations if systems face issues. This means our clients do not have to deal with poor system performance or major downtime.
Monitoring
We have various security measures and systems that continuously monitor for malicious activity, attacks, and unauthorized behavior from multiple perspectives. Our team can mitigate any potential attacks by following the internal procedure set for such events. We share our security systems, architectures, and test results with our SOC 2 auditing firm, and you can review such measures upon requesting the SOC report.
System and performance monitoring
We have various security measures and systems that continuously monitor for malicious activity, attacks, and unauthorized behavior from multiple perspectives. Our team can mitigate any potential attacks by following the internal procedure set for such events. We share our security systems, architectures, and test results with our SOC 2 auditing firm, and you can review such measures upon requesting the SOC report.
Maintenance
All scheduled and planned updates to Nakisa applications during which Subscription Services may not be available to our clients take place during our standard maintenance window over the weekend to minimize user disruption. The client will be notified of any other planned downtime in advance. Nakisa will diligently mitigate the risk of undue disruption to normal business operations. In case of emergency maintenance where Nakisa needs to make the Subscription Services unavailable to perform a maintenance operation outside of any Scheduled Downtime period, the clients will be notified of an Emergency Maintenance as soon as possible.
Nakisa SLA for support
While our configuration management process and proactive monitoring prevent most issues from affecting you, we’re prepared to respond when an event causes downtime of your system. We’re pleased to solve any issues based on our industry-standard response times. However, we understand that some issues require immediate attention. Thanks to our escalation policy, you can rest assured that the necessary resources will be allocated for a timely resolution when needed. We also perform regular tests of our disaster recovery capabilities to ensure we’re ready to respond efficiently and promptly when unplanned downtime happens.
Frequently asked questions
Robust information security policies are set in place and are enforced company-wide, as well as with contractors, and are available to our SOC 1 and SOC 2 auditors through Nakisa portals. We review these internal policies annually and communicate changes to ouremployees/contractors via internal communication portals. More details on the above policies are provided in our SOC reports.
Here are a few of our internal policies that ensure our team handles our clients’ data with the utmost security:
- Change Management Policy;
- Access Management Policy;
- Information Security Policy;
- Risk Management policy;
- Information Asset Management Policy;
- Incident Management Policy;
- Data Retention and Disposal Policy;
- Data Protection Policy;
- Data Retention and Disposal;
- Information Security Awareness Policy.
Nakisa’s approach to security is built on the shared responsibility model with leading and trusted cloud service providers. While we regularly review the third-party audit reports of our cloud service providers, internally, we share the responsibility of security controls throughout the organization, including HR, IT, CloudOPS, Products, and R&D. We leverage frameworks such as NIST CSF (National Institute of Standards and Technology Cybersecurity Framework) and CSA CCM (Cloud Security Alliance Cloud Controls Matrix) and attest to our system’s description and controls through our SOC Type 1 and SOC Type 2 reports.
Nakisa has been working on FIPS compliance for more than a decade to keep its network secure and protect its precious customer data by phasing out any non-compliant components with the ones that comply with the latest FIPS 140 standards. As such, recently, Nakisa has a dedicated release to update its Cloud Connector to stay compliant with
FIPS 140-2 standards for cryptography modules. Nakisa also offers free dedicated support to help its customers update their infrastructure to remain secure and compliant with the latest FIPS cryptography standards. Read more about our FIPS compliance here
Client data within Nakisa solutions is logically isolated and protected through layered security controls. Data is encrypted at rest and in transit using industry-standard encryption mechanisms, with encryption keys managed securely through controlled key management services. Access to client data is restricted based on defined roles and permissions, supporting privacy, confidentiality, and data protection requirements.
Nakisa’s cloud environments are designed to restrict direct public access and are hosted within isolated virtual private cloud (VPC) networks. Additional protection is provided by ACL (access control list) firewall rules that only allow traffic from specified ports to and/or from specific destinations. Access is exclusively via HTTPS and uses a reverse proxy to protect the environment from the outside world.
Data within Nakisa solutions is encrypted in transit using industry-standard secure communication protocols and encrypted at rest using robust encryption mechanisms provided by our cloud infrastructure providers. Encryption technologies and key management services are operated within the providers’ secure environments and are configured and governed in line with Nakisa’s security and data protection requirements.
Nakisa works with trusted cloud service providers to constantly monitor the environment’s security, and we’ll take necessary corrective action to mitigate the risk of intrusions. We leverage monitoring and detection tools to identify potential threats and follow our incident management processes to triage alerts and take the necessary actions.
Under Nakisa’s Access Management policy, when an issue is raised via our support ticketing system, our support team will request client approval for temporary access to investigate and resolve the issue for the specific environment/s. This access is granted for a limited time, enough to resolve the ticket with auto closure enabled by the system when access is approved.
We follow a diligent change management policy with procedures for the segregation of duties. Security is a significant component that could drive a change in our solutions to ensure that risks are treated following their evaluation. Security also evaluates changes and is a stakeholder in the change management process.
This change management process is independently assessed as part of Nakisa’s annual SOC 2 Type II audit, providing assurance over the design and operating effectiveness of related controls.
Nakisa leverages cloud infrastructure capabilities to support automated, encrypted backups within a high-availability and scalable environment. Backups are stored securely and protected through access controls and encryption, helping support data durability and recovery. Backup processes are monitored and tested in accordance with Nakisa’s business continuity and disaster recovery practices.
As per the Nakisa Incident Management policy, a support case is triggered after each security incident, whether identified through our monitoring and detection tools or by a user. This support case details the incident and flags the appropriate level of urgency. Resources are assigned as needed to each incident based on support triage.
To request any of our certifications or reports, click here. Are you considering Nakisa solutions? Reach out to our team today to get all your security questions answered!
If you’re an existing client, please contact your Account Manager for more details.
Yes. Nakisa undergoes regular independent third-party audits to validate the design and operating effectiveness of our security controls.
This includes annual ISO 27001, ISO 27017, SOC 1, and SOC 2 Type II examinations performed by an independent auditor, as well as recurring security assessments such as vulnerability testing. These audits provide assurance that Nakisa’s security controls are not only designed appropriately but are operating effectively over time.
Audit reports can be requested at /security-measure-and-compliance-reports-request/
Nakisa is designed as a secure multi-tenant SaaS platform, with controls in place to ensure that each customer’s data is logically isolated and protected from access by other tenants.
Tenant isolation is enforced through a combination of application-level access controls, logical data separation, and segmented cloud infrastructure. Each customer environment operates within clearly defined security boundaries, ensuring that data access is restricted strictly to authorized users of that tenant.
These controls are regularly assessed as part of Nakisa’s security governance and independent audits, helping ensure that customer data remains confidential, isolated, and protected at all times.
Nakisa’s SaaS solutions are hosted on leading enterprise-grade cloud infrastructure providers, selected to meet high standards for security, availability, and scalability.
Customers can choose from a list of geographic regions where their data is hosted, enabling them to meet data residency, sovereignty, and regulatory requirements. Customer data remains within the selected region unless otherwise agreed.
This regional hosting flexibility allows Nakisa to support global organizations while maintaining consistent security and compliance controls across all environments.
Yes. Nakisa supports Single Sign-On (SSO) integration with customer-managed identity providers using industry-standard authentication protocols.
This allows customers to authenticate users through their own identity systems, enforce their internal access policies, and simplify user lifecycle management. Centralized identity management also enhances security by reducing reliance on standalone credentials and supporting stronger authentication controls.
Nakisa follows a documented data retention and secure disposal process to ensure customer data is handled responsibly throughout its lifecycle.
Upon contract termination, customer data is securely deleted in accordance with contractual requirements and applicable data protection standards. This process is designed to prevent data recovery and ensure that customer information is not retained beyond its intended purpose.
Considering Nakisa solutions? Reach out to our team today to get all your security questions answered! If you are an existing client, please contact your Account Manager for more details.